02.09.2017, 17:50
Connection flood
02.09.2017, 20:12
This is different problem and it can be fixed by samp.exe (browser) update. But it's not possible without changing query system concept.
02.09.2017, 20:55
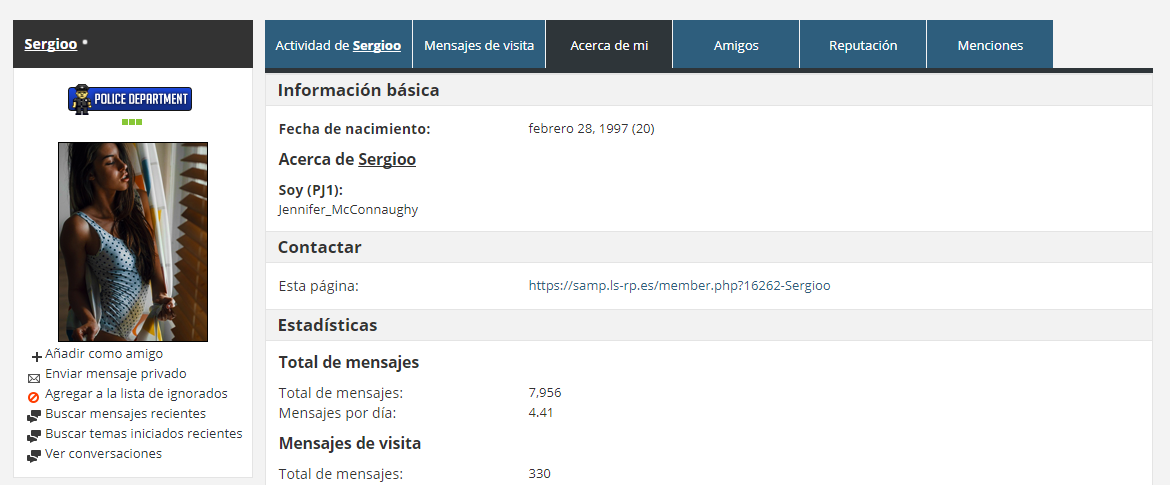
The server behind these attacks is LS-RP.es. The owner of that shit called Sergio Mengibar.
02.09.2017, 22:29
03.09.2017, 00:00
I blame him because everything that is happening is his fault. The user who uploaded a screenshot 'Jennifer_McConnaughy' is the character I told you. Sergio Mengibar. He owns booter.xyz himself. I do not speak without knowing.

I do not speak without knowing. All is true. This person is doing a lot of damage to the SA-MP world.
You currently have access to everything LS-RP.es Host the server in your dedicated OVH GAME.

I do not speak without knowing. All is true. This person is doing a lot of damage to the SA-MP world.
You currently have access to everything LS-RP.es Host the server in your dedicated OVH GAME.
03.09.2017, 00:24
0.3.7 R2-2 not stopping query flood for me
server ip: 70.42.74.3:7777
server ip: 70.42.74.3:7777
03.09.2017, 00:28
03.09.2017, 00:57
Quote:
|
I blame him because everything that is happening is his fault. The user who uploaded a screenshot 'Jennifer_McConnaughy' is the character I told you. Sergio Mengibar. He owns booter.xyz himself. I do not speak without knowing.
  I do not speak without knowing. All is true. This person is doing a lot of damage to the SA-MP world. You currently have access to everything LS-RP.es Host the server in your dedicated OVH GAME. |
03.09.2017, 01:02
(
Последний раз редактировалось adri1; 03.09.2017 в 03:16.
)
0.3.7 r2-2 don't stop query flood attack
03.09.2017, 06:18
03.09.2017, 08:27
Quote:
|
Im in same Boat as you my friend....my Debian was unmounted at all....and im still at Null Progress by all. My IP still flooded, my server still offline. I was thinking about change it to Windows, because @iLearner SV looks are working, but sometimes it is offline too, idk if he fixed at all the flood problem. IDK what more i can do, but i will search out, until i find the way to run my server again. Its funny, if i start it, in same minute some old players join it, then i look at SV CPU usage, goes to 100%, ping get high, packet loss, and finally timeout for all. So sad...nothing helps for me, i used the last Update from Kalcor, iptables rules, nothing works for me?
|
Best Regards
03.09.2017, 11:24
Quote:
|
so sorry but itsCONFIRMED 0.3.7 r2-2 don't stop query flood attack
Best Regards |
kalcor only minimized the effects caused by the attack on the server!
if you do not have enough bandwidth for the attack,
nothing that kalcor does, will help you!
this does not depend on the samp at the moment depends on your hosting company, if you have not hired any, the problem is yours!
I believe most servers are online because they have enough bandwidth!
03.09.2017, 12:12
Quote:
|
kalcor can not do anything if the attack is greater than your network can handle!
kalcor only minimized the effects caused by the attack on the server! if you do not have enough bandwidth for the attack, nothing that kalcor does, will help you! this does not depend on the samp at the moment depends on your hosting company, if you have not hired any, the problem is yours! I believe most servers are online because they have enough bandwidth! |
Ever hear, read any about backbones, Cisco12400 Router? Im right now 1 step from one! My University backbone.
Ok then tell me how much bandwidth you think i need to have? And i give you a Screenshot of my last 5GB/s test, from right now? Ok?
So can you please stop to quote me for things about you havent any knowledge? Like what bandwidth my rootserver have? Thank you
Please Back to the Roots!
03.09.2017, 12:22
Quote:
|
kalcor can not do anything if the attack is greater than your network can handle!
kalcor only minimized the effects caused by the attack on the server! if you do not have enough bandwidth for the attack, nothing that kalcor does, will help you! this does not depend on the samp at the moment depends on your hosting company, if you have not hired any, the problem is yours! I believe most servers are online because they have enough bandwidth! |
I've tested both of his patches locally with my tools and confirm his patches do NOT work, and I have a gigabit home-network. Fixing this would require an overhaul of the SA-MP querying system, which I doubt kalcor has time nor feels like doing. Get Ubi's plugin, compile it & add it to your server, this is the ONLY method that's stopped this attack.
EDIT: My mistake, the released patches were not for cookie flooding.
03.09.2017, 12:46
Quote:
|
This has nothing to do with bandwidth at all.... Actually, as explained in previous posts, this attacks recreates the connection process to the sa-mp server and abruptly stops it. In addition, with the spoofed source address, the sa-mp server is aimlessly sending cookies out to bogon IP addresses. This is a CPU based attack, bandwidth is NOT affected, this attack is less than 1-2 megabytes of packets, not even CLOSE to a real bandwidth attack. You could theoretically reach larger packet sizes but I doubt those kids know anything about real packeting.
|
03.09.2017, 14:28
(
Последний раз редактировалось dugi; 03.09.2017 в 16:51.
Причина: fixed formatting
)
Quote:
|
Believe me i have more bandwidth as you can ever buy.
Ever hear, read any about backbones, Cisco12400 Router? Im right now 1 step from one! My University backbone. Ok then tell me how much bandwidth you think i need to have? And i give you a Screenshot of my last 5GB/s test, from right now? Ok? So can you please stop to quote me for things about you havent any knowledge? Like what bandwidth my rootserver have? Thank you Please Back to the Roots! |
there is no logic since your server should be online using the UBI plugin and the Kalcor update!
I think you do not know what a DDOs attack is!
the attack received is layer 7, however with the fixes this is not a problem!
if you have enough network and hardware to support the attack your server will be online!
Because UBI in your plugin has taken the limits and kalcor has improved the query control!
that is the question,
I did the simple control using iptables,
when an ip tries to send the packets for 1 second its packets will be blocked, blocking all the first packets of the queries and cookie,
except for query i, in the case of query i I only accept the first package in the interval of 1 second,
this in theory blocks 90% of malicious packages,
after sending the first packets the client ip will be released and no longer blocked by the firewall!
a spoofed attack is not impossible to block!
all attacks are anomalies, although the packets are the same as the client samp.
Unfortunately it is not possible to see the effects of the firewall on the same server node!
ie the firewall must be placed a node earlier than the samp server is.
Example: I own a dedicated, add iptables rules in this dedicated, and create a vps and host my samp server!
in this way it will be possible to see that 90% of the attack is not redirected to the vps server, that is, blocked by iptables!
you live by saying that I do not know about things, however my servers are completely online under attack while yours is offline!
Review your concepts friend!
03.09.2017, 17:53
03.09.2017, 18:22
Quote:
|
Best thing to do is tp try to contact them, that's what people recommended me doing at least.
|
03.09.2017, 18:23
I sent a mp to kalcor but it does not respond, is there any other faster way to contact them?
03.09.2017, 18:24
I am happy to see I've both of my servers on list.
« Next Oldest | Next Newest »
Users browsing this thread: 1 Guest(s)


